The Internet of Things (IoT) industry has grown significantly in recent years. These devices are revolutionizing various sectors, contributing to their development and improving our quality of life. One of the main challenges faced by companies designing such solutions is cybersecurity.
This article outlines the steps worth taking to move toward compliance with legal requirements without waiting for consultations with certification bodies to be completed.
Legal regulations
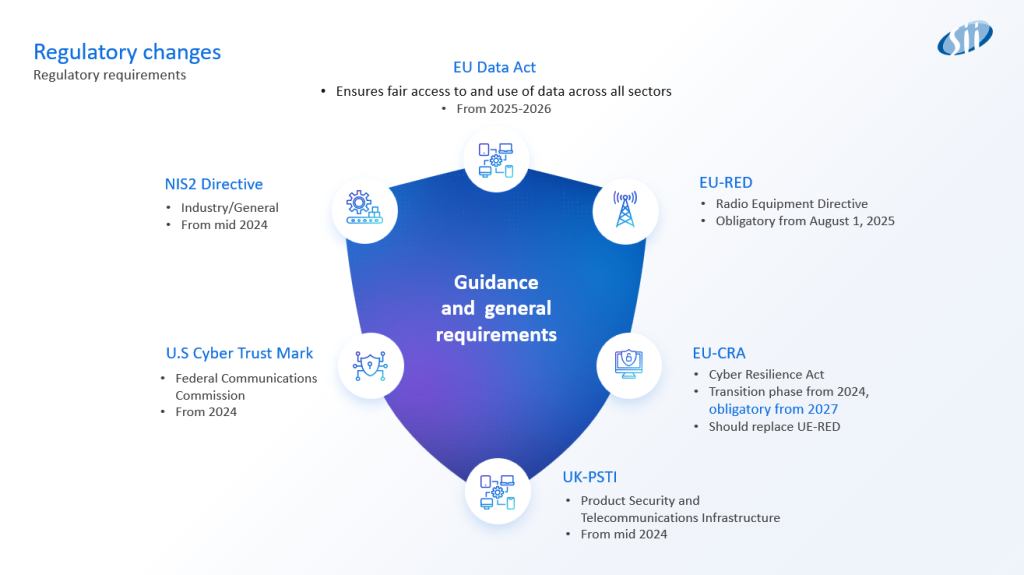
As the IoT industry evolves, new legal regulations are emerging to ensure an adequate level of security for IoT devices. These regulations introduce a range of additional obligations, rules, and principles, and companies creating products will be required to implement them.
In many cases, the regulations will only define general principles and requirements. The technical standards supporting these regulations will describe the implementation details.
A list of the regulations currently having the greatest impact on the IoT device market is shown in the figure below:
Interpreting legal regulations
When we begin reading and analyzing the content of specific legal regulations, we will certainly notice that many points are not precisely defined or described in detail. There will undoubtedly be many contentious issues and additional questions about how to meet the requirements in the context of our designed devices. In many cases, this will require consultation with certification bodies and legal teams.
Despite these challenges, by looking holistically at all upcoming legal regulations and technical standards, we can identify a group of functionalities and processes whose implementation will help us meet many requirements.
Technical solutions
The following list of functions and processes allows us to begin implementation without waiting for the completion of consultations with certification bodies and legal departments. It also enables us to take a significant step toward compliance.
Secure boot
Ensures that the device only runs software trusted by the manufacturer. This process includes cryptographic checks to verify the integrity and authenticity of the firmware before it is launched. Implementing a secure boot in IoT devices helps prevent unauthorized code from running and protects against malware and other threats.
Secure update (Over-the-air secure update)
Allows IoT devices to receive firmware updates remotely. These updates must be delivered securely to prevent tampering. Encryption and digital signatures ensure that updates are authentic and unaltered, maintaining the device’s security and functionality.
Secure manufacturing
Involves incorporating security measures during the manufacturing process. Through control and monitoring, we ensure that the produced device operates under the supervision of dedicated hardware and software components.
Vulnerability monitoring
A continuous process of identifying, assessing, and mitigating device vulnerabilities. It includes:
- Regular security assessments
- Monitoring for new threats
- Periodic source code scanning to detect reported vulnerabilities and threats
This process allows early detection of issues, providing additional time to respond before the identified threat affects device security.
Monitoring devices in the field
This function involves monitoring, diagnosing, and detecting situations in the device that should not occur under normal operating conditions. One example is observing transmission patterns for unusual request frequency or data volume. If abnormal behavior is detected, access to certain data or functions can be blocked to prevent potential issues.
Secure communication
Ensures that data transmitted between IoT devices and other systems is protected from interception and tampering. This is achieved through encryption protocols such as TLS (Transport Layer Security) and secure key management practices. Secure communication is essential for protecting sensitive data and maintaining the integrity of the IoT network.
Secure storage
Devices collect and generate large amounts of data for various purposes. This information may be considered personal or sensitive and is subject to special protection under legal regulations. Encrypting this data significantly hinders its extraction and disclosure.

Summary
Meeting all legal requirements will require implementing additional components. The points listed above will, in many cases, take the most time but will bring us closest to full compliance with our devices’ requirements.
We must understand that implementing security in products is not just a set of tasks to complete. It requires a complete shift in mindset and the creation of processes that enable the application of all security-related elements. This process will take time, preparation, and testing of various solutions to identify the most effective ones.
***
If you’re interested in Cybersecurity and IoT, check out other articles by our experts.


















































Leave a comment