Let’s start by saying what people, in general, understand about hackers: some nerds who commit digital crimes such as fraud, break the privacy of social media or applications, take control of security cameras and other types of sabotage.
In this article you going to learn:
- what is a real hacker,
- the field to develop skills,
- how to contribute in the fields of business,
- and why is so important for a corporation and attractive in the market as a professional role position.
Who is a hacker?
As in other languages, the web has a place for references, and for internet security standard documents named IETF, which explains the real term meaning of “hacker”, make references to the term “cracker”.
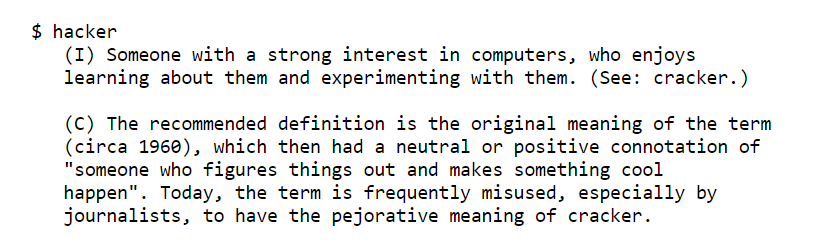
The root of the misconception started by journalists around the world confusing what actually is a profession, always points to cracker activities or attacks aka informatic pirates by hacker roles.
But many of us are influenced by magazines, movies, and maybe series as Mr Robot will teach the path of the invisible line between the ethical in the industry and the part where you can copy and paste some scripts and generate an attack without any idea about what you are doing and being involved in some wrong and illegal stuff pretty similar like an script kiddie:
A script kiddie, kiddie, or skid is a relatively unskilled individual who uses scripts or programs, such as a web shell, developed by others
Where are the hackers?
By definition, a hacker is not someone involve only in Cybersecurity, but instead someone with really good skills in IT. It can be a developer or someone who creates a machine integrating software. To understand, there are groups of people interested in developing tools or software, other groups developing improvements in the current software industry, others making the way to connect machines with humans more easily, and other groups focusing on security systems of information.
We can multiply the list of examples. Among them will be:
- the influence of typescript and what it resolves in Javascript for frontend developers,
- thinking about privacy on the internet and what Nick Mathewson made with TOR Browser,
- how blockchain was made and for what purpose,
- the latest video game which interacts with real human life,
- or the latest advance security features in your wallet virtual account.
In general, all of those things are made by hackers.
Hackers and Cybersecurity
Now, there is also another group more specific in the branch of security research whom dedicate their lives to protecting systems of information, and, something particularly I like, informatic forensics.
Basically, Cybersecurity has a bunch of roles, but imagine as in real life when occurs a crime, there is an institution of forensics implementation making the evidence as part of a scene the tale of history. Well, in the digital world occurs the same.
Let me just push on rails this little and basic sample: Someone realizes that his bank account application registers a transaction he never did, and part of his money went lost. The forensic security officer takes a line of time to track all movements in the victim case, starting by analyzing metadata, IP connections, systems log in applications, leaks by the latest input flags on websites, etc. A sort of procedure to finally mitigate and exploit the material involved and get a conclusion about who has the responsibility for the case.
There are other branches in Cybersecurity fields, which produce similar cases within a corporation with the information, and so on.
Hackers and Internet of Things
The thing is that since the Internet involved our life making us depend on almost everything, the big deal grew up and now is named IPV6. Basically, the protocol of communication which provides an identification and location system for everything you can imagine. Is named IoT, Internet of things, I called the spirit of the machines, developed by all of us. And pretty dangerous.
You might wonder why a said “dangerous”. Because his beauty is the same weakness, from the beginning nobody thought about security models and that’s why already many people are affected. In other words, now you can find a lamp for your house which is connected to the Internet. Or a house with the intelligence to open and close doors because is connected to the internet and has a public address. Or even your car and maybe the pen you use might have a little camera installed which is also is connected.
As you can see, everything is connected. And guess what? All of them are created by hackers. Beauty was created with a bunch of errors which are by default part of our life. Who says nobody else in the world can be connected to the same device you think is private because is inside your house?
Hackers and the importance of information
I guess in 2022 you know that the “information” is the “santo grail” in the digital era industry. It is the most important value in a corporation, and also for humans which for a ton of reasons, corporations hire ethical hackers to attempt to break protected systems in professional roles to practice task in Penetration testing or “Pen test” as shortcut named.
Now, the other side is about security, protecting the ecosystem of information, starting by everyone in the corporation from the physical and digital way to use and access “the information”. We contribute in a corporation without being a hacker or knowing a lot of develop software or whatever other grey matter facts, when we signup a confidential contract and we made privilege the information. As simple as because we are part of “that” ongoing information:
- our names,
- credentials,
- the bank registrations accounts,
- the number of family members register somewhere in a medical form,
- the financial or internal statistics of the company,
- the methods,
- the internal clients, etc.
What means? It means that even if you hangout a USB with some information related to the company you are responsible about the information attached, and exist protocols generated by corporations to make sure every employee can grant a good way to access and keep private the information. Nothing difficult but really important. The information is already mostly on the internet even talking about people, and just by that fact, it is vulnerable.
Everybody knows that google is the gold motor popular in the world, but not everybody knows that the engine has a special tool for research. Then talking about hackers, there is an activity named: google hacking. It’s a way to implement more sophisticated research in the input box by the browser.
Now you can understand how a simple tool like an input box text can be a powerful weapon to get information. Personally, when I did private auditoria for companies and check the status of public information on the Internet, I found a lot of PDFs and excel files with private information – just using google hacking.
Tips on how to become a hacker
Finally, become a hacker means that you are capable to generating security tools, develop policies as Cybersecurity results, keeping secure and reducing the information leaks risk, amount other skills. But education is always the best way – that’s something I personally like. This is the reason why here I wrap some advice if you are interest to start the path in security fields:
- Internet has amazing and good approaching how we can easily find education online, understand the network and protocols.
- Systems to practice and learn about it: use Kali Linux, it can provide you many tools as develop the ecosystem of defense and other laboratories.
- Make practice in free websites which offer CTF “capturing the flag”, which will help to understand the technical principles of information.
- Participate in forums and conferences around the world to understand how everything connect from the outside box is important.
- Start to generate or create new tools by your own or solutions using the current knowledge you have and how you can make better the fluid work of “something”.
And what about the benefits?
Many companies support with benefits candidates’ enhancements, proposals and majority of them offer bug bounties in several scenarios when you can provide solutions. You can ask Google: “How much can a cyber security make?” for example, in order to find some “numbers” incomes by market in security roles. The reality is that every day the industry requires more robust ways to protect the information due the number of applications.
And that’s why I refer not only to the view of security but also thinking how developers play an important role before sending code to production adding the model of design to the security facts.
Summary
Just to summarize, you already know being a hacker is more than security roles, and also know what is not. Hacking is reducing the impact of security risk by protecting a system of information and making more special applications connected with IoT. Hacking also has the side to improve the ecosystem of tools to make robust application features.
Exist many ways to become a hacker and already the Internet is the closest approach to making it and practising because the market has several needs. Internet is insecure even by definition, and the applications require to involve the security branch in the model of design.
You understand why is important the information and why you need to contribute to protecting it. If you are a developer, you have a lot of chances to create new tools to help different situations and also you have the advance to earn good profits working on it, or just playing for some time.

















































Leave a comment